Wireshark
v4.2.3 (64-bit)
By Wireshark Foundation
Date Added: 18-Feb-2024
(FREE APPLICATION)
Wireshark is Free, Open-source Network Protocol Analyzer. You Can Easily Captures All Network Traffic. Wireshark Project Started by Gerald Combs in 1998.Wireshark stands as a widely embraced network protocol analyzer, skillfully delving into real-time network traffic inspection and analysis. Its origins trace back to 1998, crafted by the talented Gerald Combs, and it has since risen to the zenith as one of the premier network sniffing utilities accessible today. Offering an open-source pedigree, Wireshark extends its welcoming arms across Windows, macOS, and Linux operating systems, without any accompanying price tag. In the realm of network administration and security analysis, Wireshark emerges as an invaluable companion. It bears the capacity to capture and scrutinize data packets coursing through networks, paving the way for network troubleshooting, security evaluations, and the debugging of network applications. With Wireshark, users dive deep into the ocean of network protocols, encompassing the likes of TCP, UDP, HTTP, DNS, and a myriad of others. Wireshark shines brightly due to its flexibility, capable of capturing packets from both wired and wireless networks. Its extensive support for various network interfaces and protocols grants it a chameleon-like adaptability, making it a true virtuoso in network analysis. Notably, it excels in both live capture and offline analysis, equipping users to either witness network traffic in real-time or dissect packets from previous encounters. Facilitating a user-friendly journey, Wireshark presents an intuitive graphical interface, rendering navigation a breeze. Captured packets are elegantly displayed with a judicious use of color-coding, enabling users to effortlessly distinguish between different packet types. The tool's packet filtering capabilities, allowing for precise criteria-based filtration like protocol, source and destination IP addresses, ports, and more, further enhance its utility. At the heart of Wireshark's prowess lies its ability to decode and analyze network protocols across various layers of the OSI model, spanning from the physical layer up to the application layer. It possesses the acumen to decipher a diverse array of protocols, encompassing Ethernet, TCP, UDP, HTTP, DNS, and even encrypted protocols like SSL/TLS, unfurling the encrypted traffic for users' scrutiny. Wireshark's arsenal includes an array of potent tools that empower users in the analysis of network traffic. The 'Follow TCP Stream' feature, for instance, enables the viewing of complete TCP streams for specific connections, while the 'Statistics' feature furnishes comprehensive insights, from packet and byte counts to protocol distribution and beyond. To cherry-pick and spotlight specific packets or traffic patterns, users can leverage Wireshark's display filters. Notably, Wireshark isn't exclusive to network administrators and security analysts; developers too find it indispensable for debugging network applications. It allows developers to plumb the depths of network traffic, rooting out communication hiccups in their applications. Furthermore, it equips them with potent tools for dissecting network protocols, like the 'Protocol Hierarchy' feature that unveils the layered protocol stack within each packet. In the realm of security analysis, Wireshark emerges as an indomitable ally, primed for the detection and analysis of network-based attacks. It lays bare network traffic for security analysts to identify irregular or malevolent traffic patterns, unmasking network-based malware like viruses, trojans, and worms. Moreover, it unearths network-based vulnerabilities, such as misconfigured firewalls and unencrypted traffic. Nonetheless, it's important to note that Wireshark, like any potent tool, can be wielded for nefarious purposes. Malefactors can employ it to capture and scrutinize network traffic, potentially pilfering sensitive information, such as passwords and financial data. Thus, the responsible and ethical use of Wireshark is paramount. Ethical use of Wireshark entails a thorough comprehension of the objectives behind network analysis or security work. This necessitates securing necessary permissions, like written consent or legal clearance, prior to deploying Wireshark for packet capture or analysis. Additionally, any data captured must be vigilantly protected and securely stored to thwart unauthorized access and data breaches. Equally crucial is the avoidance of capturing or analyzing sensitive data, such as personally identifiable information or confidential business data, unless done in a controlled environment fortified with stringent security measures. Furthermore, to wield Wireshark effectively, one must cultivate a profound understanding of network protocols and their intricate interplay. Familiarity with the OSI model, its layers, and various network traffic types, including TCP, UDP, and HTTP, is a prerequisite. For those eager to embark on a journey of discovery with Wireshark, practical experience in a real-world network scenario can be transformative. Establishing a small test network and employing Wireshark for traffic capture and analysis serves as an invaluable learning experience. In addition, a wealth of online resources, ranging from tutorials and documentation to user forums, stands ready to assist those seeking to master the art of Wireshark. In summation, Wireshark emerges as a formidable and adaptable network protocol analyzer, gifting users an expansive toolkit for capturing, analyzing, and debugging network traffic. Yet, ethical usage is imperative to ensure it remains a force for good, adhering to legal and moral standards. With its myriad features and potent analytical tools, Wireshark becomes an indispensable companion for anyone navigating the realms of network analysis and security. Some of the main features of Wireshark are: Capturing: Wireshark can capture network traffic in real-time from various network interfaces, such as wired and wireless interfaces, and supports various capture file formats. Filtering: Wireshark provides a powerful filtering mechanism that allows users to filter packets based on various criteria such as protocol, source IP address, destination IP address, port number, and many more. Displaying: Wireshark has a user-friendly GUI that displays captured packets in a clear and concise manner, with color coding to distinguish between different types of packets. Decoding: Wireshark can decode and analyze a wide range of network protocols, from the physical layer all the way up to the application layer, including TCP, UDP, HTTP, DNS, and many others. Reassembling: Wireshark can reassemble fragmented packets and display the entire packet contents. Following TCP stream: Wireshark allows users to follow the entire TCP stream for a particular connection, which can be useful in debugging network applications. Graphing: Wireshark provides a built-in graphing feature that can be used to visualize and analyze network statistics, such as packet rates and protocol distribution. Coloring: Wireshark provides a powerful coloring feature that allows users to customize how packets are displayed in the GUI based on different criteria, such as protocol or packet type. Exporting: Wireshark allows users to export captured packets in a wide range of formats, such as CSV, XML, and plain text, which can be useful for further analysis. Statistics: Wireshark provides a range of statistics about the captured traffic, including packet and byte counts, protocol distribution, and many more. Expert Info: Wireshark provides expert information about the captured packets, which can help users identify potential problems and issues. Scripting: Wireshark supports scripting using Lua, allowing users to create custom dissectors and automate various tasks. Live capture and offline analysis: Wireshark supports live capture and offline analysis, allowing users to capture packets in real-time or analyze previously captured packets. Remote capture: Wireshark can capture packets from remote network interfaces using a variety of capture methods. Multi-platform support: Wireshark is available for Windows, macOS, and Linux operating systems, providing a consistent user experience across platforms. SSL/TLS decryption: Wireshark can decrypt SSL/TLS traffic, allowing users to analyze the encrypted traffic. VoIP analysis: Wireshark provides a range of features for analyzing VoIP traffic, including packet decoding and RTP analysis. Network statistics: Wireshark provides a range of network statistics, including packet rate, data rate, and protocol distribution, allowing users to analyze and optimize network performance. Wireshark plugins: Wireshark provides a plugin architecture that allows users to extend the functionality of the tool with custom plugins. Integration with other tools: Wireshark can integrate with other tools, such as Snort, to provide a more comprehensive network analysis solution. Overall, Wireshark is a powerful and versatile network protocol analyzer that provides users with a wide range of features to capture, analyze, and debug network traffic. With its user-friendly GUI, support for a wide range of protocols, and powerful analysis tools, Wireshark is an essential tool for anyone involved in network analysis or security. 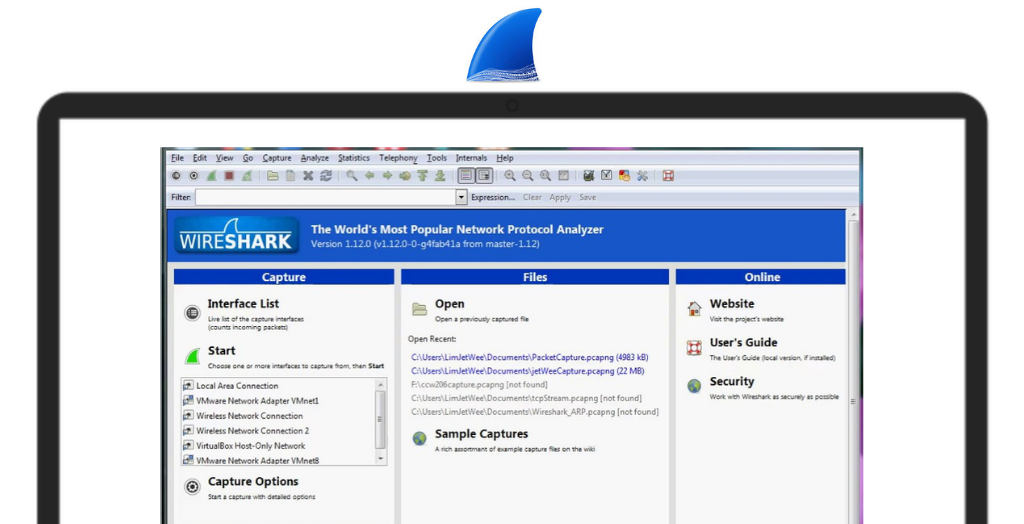
System Requirements:
Windows 8 / Windows 10 / Windows 11
Date Added:18-Feb-2024 License:Free Developer By:Wireshark Foundationhttps://www.wireshark.org/ |
Relative Softwares |
|---|